
Turn learning into fun
Teachers can create exciting, interactive learning experiences with our intuitive touchscreens. Use our interactive displays with your teaching software of choice, let your students share their device, write down the smartest ideas and inspire everyone in the classroom.

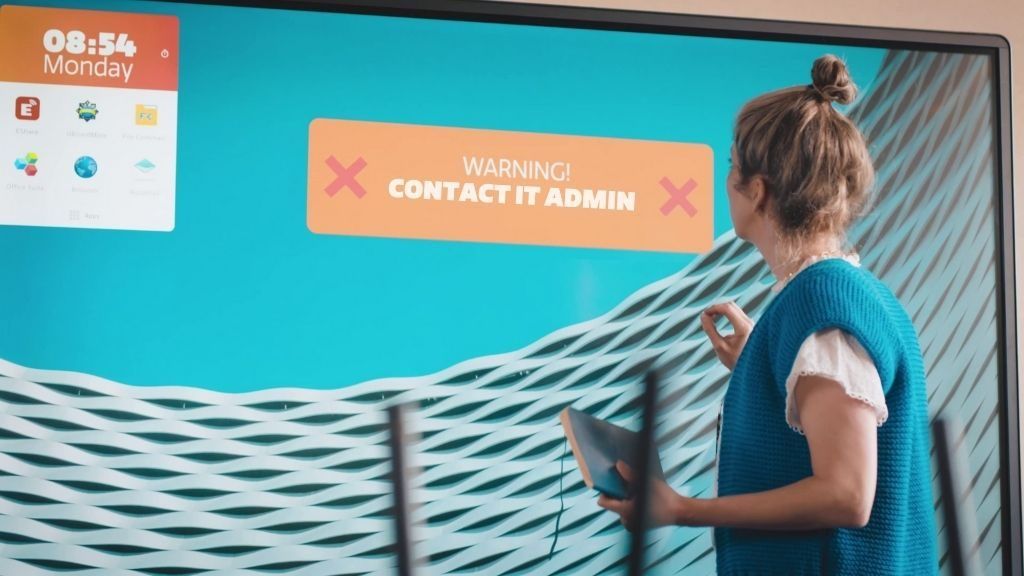
No more teaching disruptions
We know teachers rely on their interactive display to... well, teach. Can’t have classes with an out-of-date touchscreen now can you? That’s why we introduced our Heartbeat As-A-Service programme. Enrol your displays and empower IT admins to remotely and easily resolve issues and keep screens always up-to-date.
Looking for our
business products?
Sustainability
impact, together
SAFE and secure
secure environment
Customer engagement
touch and our story
Future proof
now and in the future
Classroom of the future Trends, tips & how-to's for the modern school
Blended classrooms
Bye Bye Hackers
Trends in higher education


Request your
free demo
Try before you buy! Our touchscreen demonstrations are
not only informative and inspiring, they’re also pretty fun.


SUSTAINABILITY THROUGH TRANSPARENCY
CTOUCH is the most sustainable touchscreen manufacturer in the world. Our aim is to make real and significant impact. We take responsibility for our actions by ensuring total transparency. To this end, we provide insight into the results of our sustainability mission.

Touchscreens
made for your classroom
Happy schools and
their ctouch experience

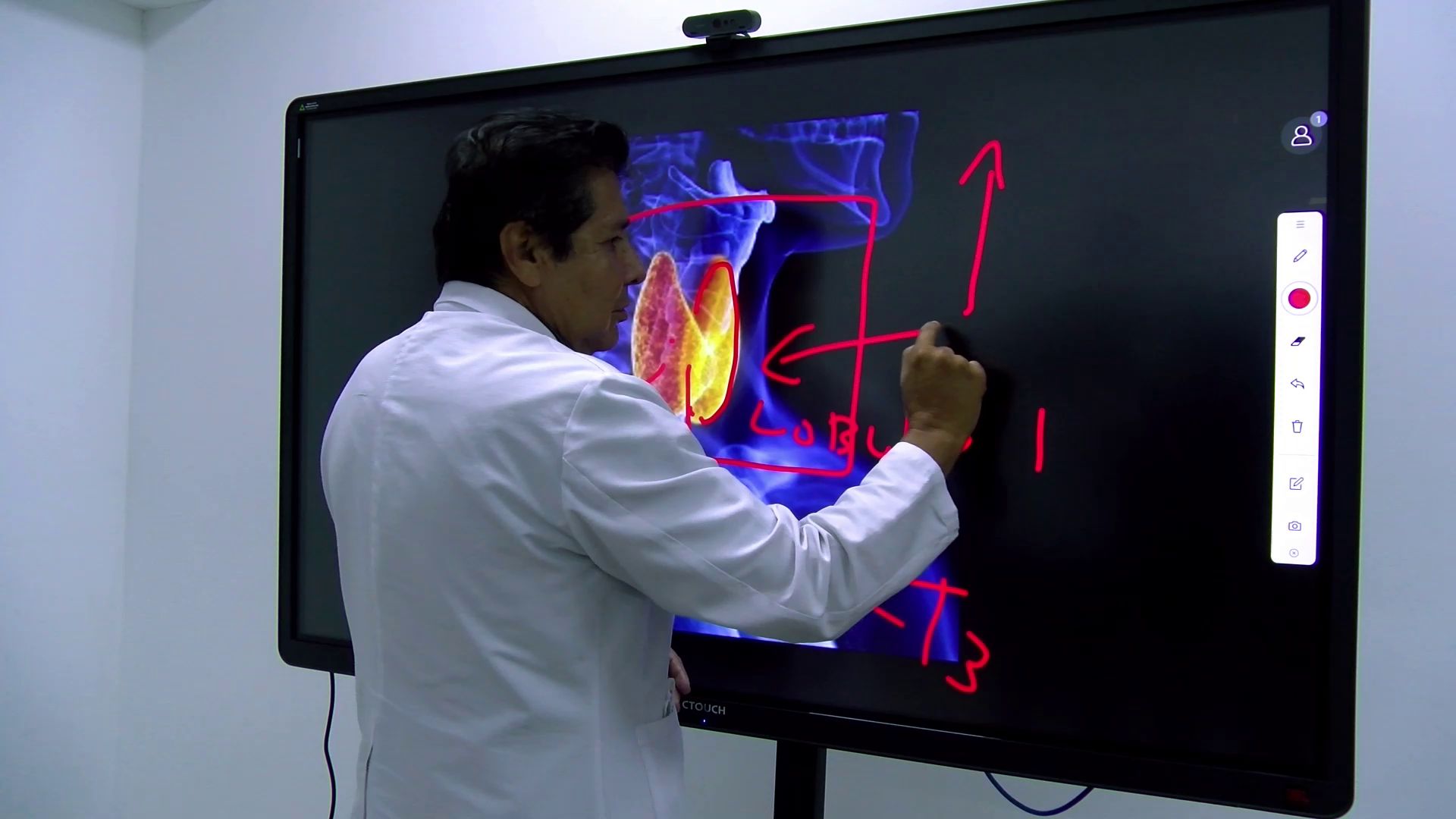
University ULEAM is in good hands with CTOUCH Riva

Why the Riva touchscreens can't be missed at the Zarduna Schule

Get in touch
with us
The CTOUCH bunch are here to help you out!
How can we be of service?


